
Table of Contents
Introduction to Cloud Privilege Escalation Detection
Cloud privilege escalation detection has become a critical focus area as cloud computing increasingly shapes how organizations, universities, startups, and government institutions in India manage data, applications, and digital services. Modern institutions now depend on cloud platforms for research computing, student information systems, digital libraries, virtual laboratories, and large-scale data analytics. While this shift has significantly improved efficiency, collaboration, and accessibility, it has also introduced complex cybersecurity risks that traditional security mechanisms are often unable to handle effectively.
A major security concern in cloud environments is insider threats—attacks carried out by individuals who already possess legitimate access to systems and sensitive data. Unlike external attackers who must breach security defenses, insiders operate within the system and can misuse their authorized privileges. This makes insider-driven attacks particularly difficult to detect using conventional tools such as firewalls, password authentication, or basic intrusion detection systems. As a result, modern cloud infrastructures require intelligent security mechanisms that can analyze user behavior rather than simply verifying login credentials.
Another serious challenge is privilege drift, where users gradually accumulate unnecessary access rights over time without periodic review or role-based reassignment. For instance, a student intern who later becomes a permanent employee may retain outdated system permissions that no longer align with their current responsibilities. Such lingering privileges create opportunities for intentional or accidental misuse. A robust cloud privilege escalation detection framework can continuously monitor access behavior, detect anomalies, and prevent unauthorized actions before they result in data breaches or system compromise.
Machine learning plays a vital role in strengthening cloud security by processing vast amounts of user activity logs and identifying subtle behavioral deviations that may signal malicious intent. Instead of relying on fixed security rules, machine learning models learn from historical data, recognize patterns, and adapt to emerging threats in real time. This data-driven approach makes cloud privilege escalation detection more accurate, scalable, and practical for real-world cloud deployments, ultimately enhancing trust, reliability, and security in digital ecosystems.
Objectives of Cloud Privilege Escalation Detection
1. Detect Insider Threats in Cloud Environments
The primary goal is to design an intelligent system that can identify insider threats automatically. Since insiders already possess valid credentials, traditional security tools fail to distinguish normal users from malicious ones. A machine-learning-based cloud privilege escalation detection system can analyze behavior patterns such as unusual login times, excessive file downloads, or suspicious data transfers.
2. Identify and Classify Privilege Escalation Attacks
The system aims to classify attacks into two major categories:
- Horizontal privilege escalation – when a user accesses data belonging to another user with similar access rights.
- Vertical privilege escalation – when a user illegally gains administrator-level privileges.
Accurate classification helps security teams take appropriate action based on the severity of the threat.
3. Apply Machine Learning for Insider Attack Detection
Supervised machine learning models are trained using historical insider threat datasets such as CERT. These models learn patterns of both normal and malicious behavior, enabling automated threat detection without human intervention.
4. Compare Multiple Machine Learning Models
Four major algorithms are evaluated:
- Random Forest
- AdaBoost
- XGBoost
- LightGBM
This comparison helps identify the most effective model for cloud privilege escalation detection.
5. Use Ensemble Learning for Better Accuracy
Instead of relying on a single algorithm, multiple models are combined using ensemble learning. This improves accuracy, reduces false alarms, and increases reliability.
6. Achieve High Detection Accuracy
The system aims for accuracy above 95% while keeping false positives low so legitimate users are not wrongly flagged.
7. Strengthen Cloud Data Protection
By detecting privilege misuse early, the system helps prevent data breaches, financial losses, and unauthorized access.
8. Build a Customized Insider Threat Dataset
A custom dataset is created by merging multiple CERT files to better represent real-world attack scenarios.
9. Support Regulatory Compliance
The system assists organizations in meeting cybersecurity regulations such as GDPR, HIPAA, and ISO 27001.
10. Provide a Scalable Security Solution
The final framework is designed to be deployed in real cloud platforms such as AWS, Azure, or Google Cloud.
Problem Statement
Cloud computing environments face growing risks from insider attacks that exploit weak access controls and monitoring gaps. Many organizations rely heavily on identity verification but lack behavioral monitoring systems that can detect misuse of privileges. This leads to delayed detection of insider threats, sometimes months after the actual breach.
Insiders can intentionally or unintentionally misuse their access, resulting in stolen data, system manipulation, or service disruption. The difficulty lies in distinguishing normal job functions from malicious behavior. For example, a data scientist downloading large files may be legitimate—or it may indicate data theft.
To address this issue, this research proposes a machine-learning-driven cloud privilege escalation detection system that continuously analyzes user activity logs and identifies suspicious behavior patterns.
From a societal perspective, improved cybersecurity protects individuals from identity theft, financial fraud, and privacy violations. Environmentally, preventing cyber incidents reduces the energy and computing resources required for breach investigations and system recovery.
Legally, organizations benefit from stronger compliance with data protection laws. Operationally, early detection allows faster incident response, minimizing damage and financial loss.
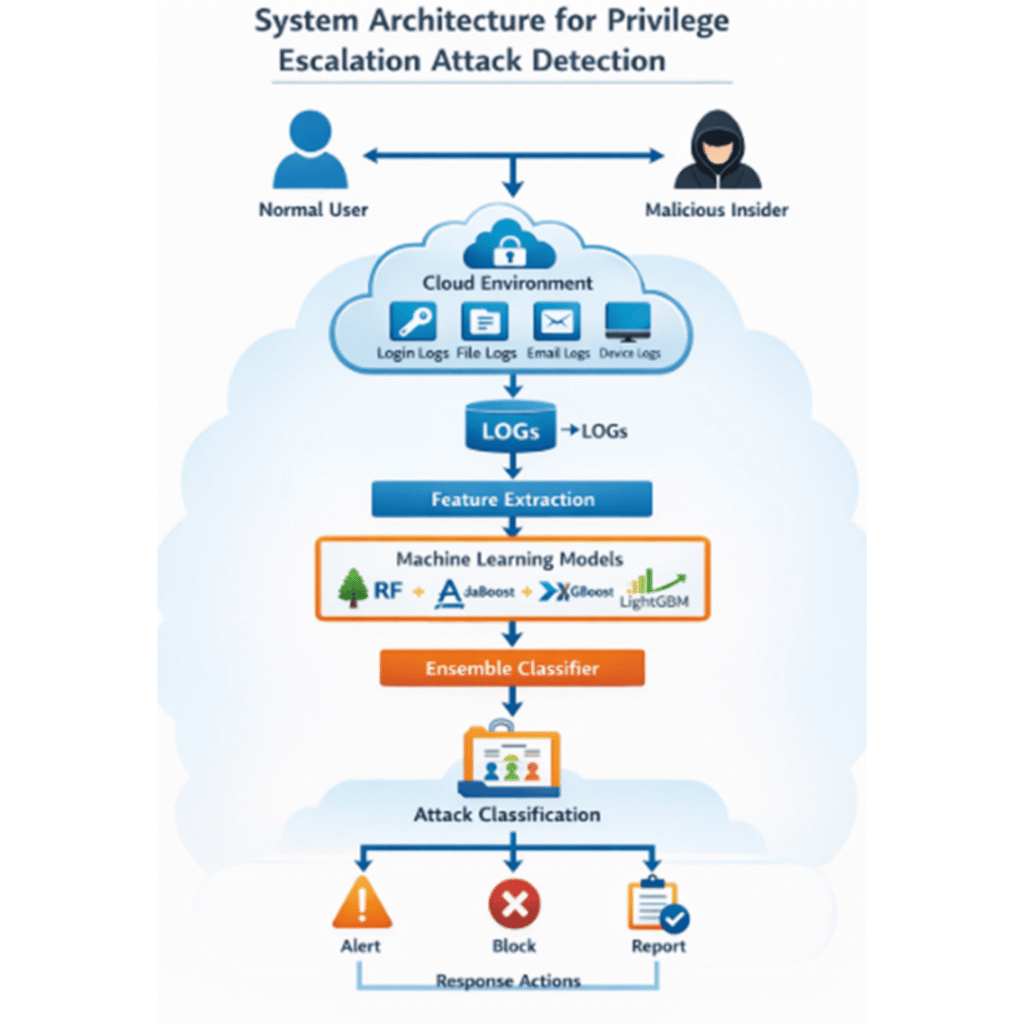
Proposed Methodology for Cloud Privilege Escalation Detection
1. Data Collection
A customized dataset is created by merging multiple CERT insider threat files containing:
- Login records
- File access logs
- Email activity
- Device usage
- System commands
2. Data Preprocessing
To improve data quality:
- Irrelevant attributes like employee IDs are removed
- Missing values are filled using statistical methods
- Extreme outliers are corrected
- Data is normalized for consistency
3. Feature Selection
Only security-relevant features are retained, such as unusual login behavior, file transfers, and privilege changes.
4. Model Selection
Four machine learning models are used:
- Random Forest
- AdaBoost
- XGBoost
- LightGBM
5. Training and Testing
The dataset is split into training and testing sets to evaluate performance objectively.
6. Parameter Tuning
Model parameters such as learning rate, tree depth, and number of estimators are optimized using cross-validation.
7. Ensemble Learning
Predictions from all four models are combined to create a stronger cloud privilege escalation detection system.
8. Attack Classification
The system labels each activity as:
- Normal behavior
- Horizontal privilege escalation
- Vertical privilege escalation
9. Performance Evaluation
LightGBM achieved the highest accuracy of 97%, while other models contributed to detecting specific attack types.
10. Deployment
The final model can be integrated into real-time cloud monitoring tools.
Expected Outcomes of Cloud Privilege Escalation Detection
1. Accurate Insider Threat Detection
The system reliably distinguishes between normal and malicious behavior.
2. Reliable Attack Classification
Organizations can clearly identify whether an attack is horizontal or vertical.
3. High Accuracy
Ensemble learning ensures accuracy above 95%.
4. Reduced False Alarms
Legitimate users are not mistakenly flagged.
5. Early Detection
Security teams can act before major damage occurs.
6. Stronger Cloud Security
Continuous monitoring improves overall protection.
7. Regulatory Compliance
Supports GDPR, HIPAA, and ISO 27001 requirements.
8. Scalability
Works efficiently even in large cloud environments.
9. Increased Trust in Cloud Services
Organizations and users feel safer using cloud platforms.
System Architecture
Conclusion
Cloud privilege escalation detection has emerged as a crucial component of modern cloud cybersecurity analytics as organizations increasingly rely on cloud platforms to store and manage sensitive data. This study demonstrates that traditional security mechanisms alone are insufficient to counter insider threats in cloud environments, particularly when attackers exploit legitimate access privileges through horizontal privilege escalation or vertical privilege escalation techniques. By leveraging machine learning for cloud security, organizations can move beyond rule-based defenses and adopt intelligent, data-driven protection strategies that continuously monitor user behavior and system activity.
The integration of insider threat detection in cloud systems using advanced algorithms such as Random Forest, AdaBoost, XGBoost, and LightGBM proves that machine learning can effectively distinguish between normal and malicious behavior. Among these models, LightGBM showed superior performance, achieving the highest detection accuracy, while other models contributed valuable insights for identifying specific attack patterns. Furthermore, the use of ensemble learning for cybersecurity enhanced overall system reliability, reduced false positives, and improved classification performance across diverse attack scenarios.
This research highlights that proactive cloud privilege escalation detection is not only a technical necessity but also a critical requirement for regulatory compliance, data privacy protection, and organizational resilience. By implementing scalable, automated, and intelligent security frameworks, cloud service providers and enterprises can significantly reduce the risk of insider-driven breaches, safeguard sensitive information, and strengthen trust in cloud-based digital ecosystems.
Ultimately, this work establishes a strong foundation for future advancements in machine-learning-driven cloud security, encouraging further research on real-time detection systems, adaptive threat modeling, and integrated defense mechanisms that can dynamically evolve alongside emerging cyber threats.
What is Cloud Privilege Escalation Detection?
Cloud privilege escalation detection is an automated security process that uses machine learning to monitor user behavior, analyze system logs, and identify unauthorized attempts to gain higher access privileges in cloud environments.
Why is insider threat detection important?
Because insiders already have access, they can cause severe damage if they misuse privileges.
How does machine learning help?
It identifies hidden patterns that traditional security tools cannot detect.
What is horizontal privilege escalation?
Unauthorized access to another user’s data at the same privilege level.
What is vertical privilege escalation?
Illegally gaining administrator rights.
Which algorithm performed best?
LightGBM achieved the highest accuracy of 97%.
Can this be used in real cloud systems?
Yes, it can integrate with AWS, Azure, and Google Cloud monitoring tools.


