Table of Contents
Abstract
Searchable Public Key Encryption is emerging as a critical solution in the era of rapidly expanding cloud computing and online storage platforms, which have transformed data management while also introducing serious security and privacy risks. Organizations and individuals increasingly store confidential information on third-party servers, raising concerns about unauthorized access, data leakage, and misuse. Conventional encryption techniques protect data confidentiality but make encrypted information difficult to search, analyze, or retrieve efficiently. This creates a usability barrier that limits the practical value of secure storage systems.
To address this challenge, Searchable Public Key Encryption provides a secure mechanism that allows encrypted data to remain protected while still supporting controlled search and retrieval operations. Instead of decrypting entire datasets, authorized users can retrieve relevant encrypted files through secure search techniques without exposing sensitive content to untrusted servers.
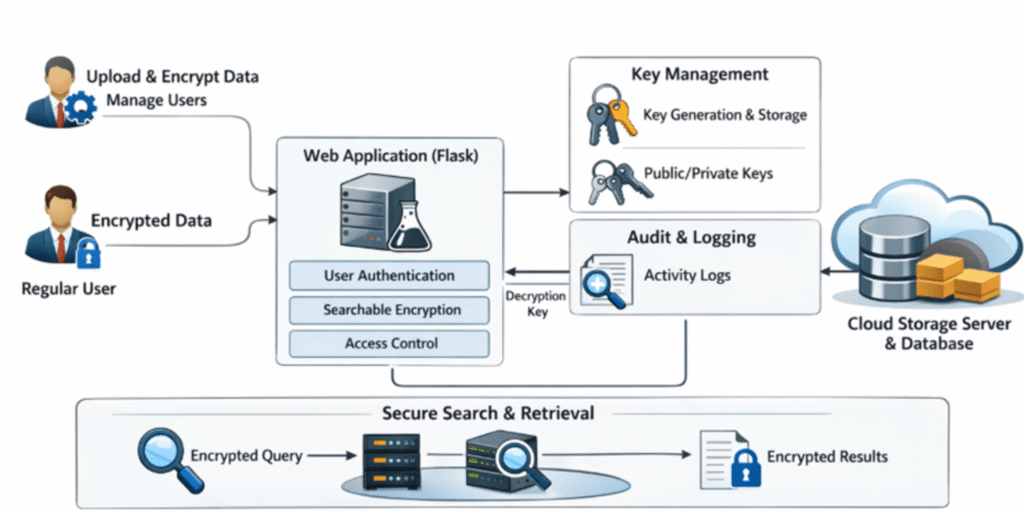
The proposed framework combines public key infrastructure with hybrid encryption to balance security and performance. Symmetric encryption secures large files efficiently, while public key cryptography ensures safe key distribution and eliminates the risks of shared secret keys. Role-based access control differentiates privileges between administrators and regular users, preventing unauthorized actions and privilege misuse.
Additionally, the system integrates real-time activity logging to record encryption, decryption, and unauthorized access attempts, strengthening accountability and auditability. This approach makes Searchable Public Key Encryption particularly suitable for cloud-based document storage, healthcare records, academic research repositories, and secure enterprise data management systems.
Introduction
The digital revolution has significantly increased the reliance on cloud computing, web applications, and online data storage services. Universities, research institutions, startups, and enterprises now depend on remote servers to store large volumes of sensitive data due to scalability, accessibility, and cost efficiency. However, outsourcing critical information to external platforms creates serious security concerns related to data ownership, privacy, and unauthorized access.
Traditional encryption techniques protect data from direct exposure, but they also make encrypted content unusable for search and analysis. Users must decrypt entire datasets even when they need only a small portion of the information, which increases computational overhead and security risks. This limitation creates a conflict between security and usability in modern cloud environments.
Searchable Public Key Encryption resolves this issue by allowing secure search over encrypted data while preserving confidentiality. With public key cryptography, data is encrypted using a recipient’s public key, ensuring that only the corresponding private key holder can decrypt it. Meanwhile, privacy-preserving search mechanisms enable users to retrieve specific encrypted files without revealing plaintext information to the cloud server.
The proposed web-based system integrates asymmetric encryption for secure key exchange and symmetric encryption for efficient data storage. It also incorporates role-based access control, distinguishing administrative privileges from regular user operations. A comprehensive monitoring system records all system activities, ensuring transparency and security compliance.
By combining cryptographic security with controlled access and auditing, this implementation of Searchable Public Key Encryption offers a scalable and practical solution for secure cloud-based data storage and retrieval.
Problem Statement
Cloud-based storage systems have become essential for academic, corporate, and personal data management, yet they remain vulnerable to security threats such as data breaches, insider attacks, and unauthorized access. Sensitive information including research documents, financial records, and medical data is frequently stored on third-party servers that cannot be fully trusted.
Traditional encryption methods safeguard data but prevent efficient searching within encrypted datasets. Users are often forced to decrypt large volumes of data even for simple queries, leading to inefficiencies and increased security risks. This limitation makes conventional encryption unsuitable for real-world applications requiring both security and usability.
Many existing systems also lack fine-grained role-based access control and proper monitoring mechanisms. Unauthorized users may attempt to access restricted files without detection due to weak logging frameworks. Furthermore, poor key management in multi-user environments increases the risk of large-scale data compromise.
These challenges highlight the need for Searchable Public Key Encryption, which enables secure encrypted search, controlled access, reliable key management, and real-time activity monitoring. The goal is to develop a system that ensures confidentiality while maintaining usability in modern cloud environments.
Objectives
The primary objective of this project is to design and implement a robust Searchable Public Key Encryption system that enables secure storage, controlled access, and efficient retrieval of encrypted data in multi-user environments.
A key focus is to integrate public key infrastructure with hybrid encryption, ensuring strong security without sacrificing performance. Each user is assigned a unique cryptographic identity, preventing key sharing and minimizing security risks.
The system also implements role-based access control, clearly separating administrative and user privileges. Administrators manage data encryption and system operations, while users access only authorized content.
Additionally, the project aims to incorporate detailed logging and monitoring mechanisms to track all system activities, including encryption, decryption, login attempts, and unauthorized access events. This enhances accountability, auditability, and overall security.
System Requirements
Software Requirements
- Operating System: Windows, Linux, or macOS
- Programming Language: Python 3.x
- Web Framework: Flask
- Database: MySQL
- Cryptographic Library: Python Cryptography
- Frontend: HTML, CSS, JavaScript
- Browser: Chrome, Firefox, or Edge
In this environment, Searchable Public Key Encryption operates as a secure web application.
Hardware Requirements
- Processor: Intel i3 or higher
- RAM: Minimum 4 GB
- Storage: 20 GB free space
- Network: Stable internet
These specifications support efficient execution of Searchable Public Key Encryption operations.
Functional Requirements
- Secure user authentication
- Automatic key pair generation
- Encrypted file storage
- Authorized decryption only
- Role-based access control
- Secure activity logging
Non-Functional Requirements
- High data confidentiality
- Reliable performance
- Scalability for multiple users
- User-friendly interface
Existing System
Traditional encrypted storage systems primarily focus on confidentiality but neglect usability. Once data is encrypted, users cannot perform keyword searches without full decryption, making data retrieval inefficient. This limitation significantly reduces system practicality.
Most cloud-based storage platforms rely on trust-based security models, assuming that service providers will not misuse stored data. However, internal threats, cyberattacks, and legal risks can compromise confidentiality. Without Searchable Public Key Encryption, users lose control over their data.
Additionally, existing systems often lack role-based access control, allowing users to access data beyond their intended permissions. Poor key management practices further weaken security, as shared symmetric keys are commonly used across multiple users.
Another major drawback is the absence of real-time monitoring and auditing. Unauthorized access attempts frequently go undetected due to insufficient logging mechanisms.
These limitations justify the need for a more secure, scalable, and searchable encryption model like Searchable Public Key Encryption.
Proposed System
The proposed system implements Searchable Public Key Encryption to enable secure cloud storage and controlled data retrieval. It integrates hybrid encryption, role-based access control, secure key management, and real-time auditing.
Each user receives a unique public–private key pair during registration. The public key encrypts data, while the private key remains confidential to the user. This eliminates shared keys and enhances security.
Data is encrypted using a fast symmetric algorithm (AES), and the encryption key is secured using the user’s public key. Even if the cloud server is compromised, attackers cannot access plaintext data.
A controlled decryption mechanism ensures that only authorized users can decrypt files. Any unauthorized attempt is automatically blocked and logged.
The system also supports privacy-preserving search, allowing users to retrieve encrypted files without exposing sensitive content.
Overall, this approach makes Searchable Public Key Encryption ideal for secure academic and enterprise data management.
Methodology
System Design Approach
The system follows a modular and security-driven development model, ensuring separation of cryptographic logic from application logic.
Cryptographic Framework
A hybrid encryption model is used:
- Public key encryption for secure key exchange
- Symmetric encryption for fast data protection
This structure supports Searchable Public Key Encryption efficiently.
Key Management
Each user receives a unique RSA key pair upon registration. Public keys are stored securely, while private keys remain confidential.
Authentication & Authorization
Two-layer security is implemented:
- Authentication verifies identity
- Authorization enforces role-based permissions
Secure Storage & Retrieval
Only encrypted data is stored in the database. Search queries operate on encrypted metadata, preserving privacy.
Audit Logging
All activities—login, encryption, decryption, and failed access—are logged securely for accountability.
System Architecture
The architecture follows a three-tier model:
- Presentation Layer – Web interface built with Flask, HTML, CSS, and JavaScript.
- Application Layer – Handles Searchable Public Key Encryption, authentication, and access control.
- Data Layer – MySQL database storing encrypted files, keys, and logs.
This layered structure enhances security, scalability, and maintainability.
Conclusion
This project successfully demonstrates the feasibility of Searchable Public Key Encryption for secure cloud data storage and retrieval. By integrating hybrid encryption, role-based access control, and secure auditing, the system achieves a strong balance between security and usability.
The implementation proves that encrypted search is practical and efficient for real-world applications, including academic research, healthcare, and enterprise data management.
While further enhancements such as multi-keyword search and blockchain-based logging can be explored, the current system provides a solid foundation for secure cloud computing.
Future Scope
Future improvements include:
- Advanced keyword-based encrypted search
- Multi-user data sharing via attribute-based encryption
- Blockchain-based immutable audit logs
- Cloud-native deployment with containerization
- AI-driven threat detection
- Mobile app support
These enhancements will make Searchable Public Key Encryption even more powerful and scalable.
What is Searchable Public Key Encryption?
Searchable Public Key Encryption is a cryptographic technique that allows users to search and retrieve encrypted data stored on cloud servers without decrypting it or exposing sensitive information to the server.
How It Works (Step-by-Step)
Each user receives a unique public–private key pair.
Data is encrypted using a fast symmetric key.
The symmetric key is encrypted using the recipient’s public key.
The encrypted file and encrypted key are stored in the cloud.
Users perform secure searches without revealing plaintext data.
Only authorized users can decrypt and access their files.
This ensures privacy, usability, and secure cloud data management.
What is Searchable Public Key Encryption?
It allows secure search over encrypted cloud data without revealing plaintext.
Why is it needed?
Traditional encryption prevents search, reducing usability.
How does it work?
It uses hybrid encryption and public keys for secure access.
Is it safe against hackers?
Yes, as private keys are never stored on servers.
Can multiple users access data?
Yes, through role-based access control.
Where can it be used?
Cloud storage, healthcare, banking, and research systems.